Data protection in research data management
06/03/2017

There was a young man we’ll name Paul,
Who answered a short survey call.
He provided his data
And was shocked to see later,
His age, faith, and health shared with all.
This limerick is definitely an example of what not to do! If you’ll be collecting any personal data or sensitive personal data during your research project, you will need to work carefully to ensure participant involvement is correctly handled, in compliance with the Data Protection Act.
Before anything else, ask yourself: do you even really need to collect personal data? Does it really hold research value or are you collecting it for administrative purposes? If personal data does need to be collected, store it separately from the research data. Consent, anonymisation, and encryption are a few other key areas to think about, when considering your data protection responsibilities.
- Consent: You must inform participants about how personal data will be used, stored, processed, transferred and destroyed. Apart from a few legal exceptions, data can only be shared with explicit consent, ideally in written form, so make sure you ask for the relevant consent for your project. See more on the ethics intranet pages including a sample consent form (docx). It can be time-consuming or even impossible to return to participants for further consent later on, so it’s important to think about the consent form wording carefully at the start; don’t hesitate to get in touch to discuss this for your project.
- Anonymisation: You are encouraged to publish your research findings and also the data underpinning them, but you must do so responsibly. Personal data should be anonymised as far as possible (e.g. removing key personal identifiers, hiding outliers, aggregating data) so that it can be shared – but you should still have obtained consent for this. Anonymising data allows it to be re-used for wider purposes than that originally specified, enhancing the value of the data.
- Encryption: This means that files are stored in an encrypted area, and can only be read with the use of a passphrase to access the contents. Microsoft Office software has an in-built encryption feature under File > Protect. If you’re collecting sensitive personal data, it must be stored with encryption, in line with ICO recommendations, to ensure compliance with the Data Protection Act. IT Services can provide encryption software and support.
As these areas relate to both research ethics and legal requirements, it is important to get these right. Participants should be confident in our practices, and good planning in these areas should also ensure no slip-ups that could cause problems for you when publishing findings. Just recently there was actually a retraction for a paper due to concerns over lack of consent from participants.
For more support on data protection in RDM, see the ICO online guide or the RDM intranet site, or email me for support at researchdata@cranfield.ac.uk.
Public domain image from MorgueFile.com
Categories & Tags:
Leave a comment on this post:
You might also like…
Keren Tuv: My Cranfield experience studying Renewable Energy
Hello, my name is Keren, I am from London, UK, and I am studying Renewable Energy MSc. My journey to discovering Cranfield University began when I first decided to return to academia to pursue ...
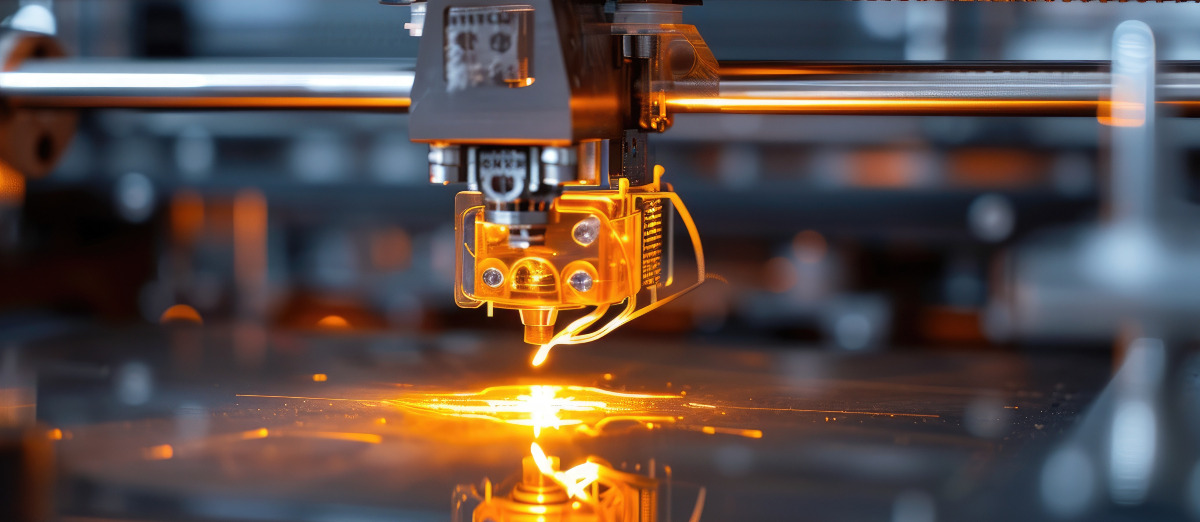
3D Metal Manufacturing in space: A look into the future
David Rico Sierra, Research Fellow in Additive Manufacturing, was recently involved in an exciting project to manufacture parts using 3D printers in space. Here he reflects on his time working with Airbus in Toulouse… ...
A Legacy of Courage: From India to Britain, Three Generations Find Their Home
My story begins with my grandfather, who plucked up the courage to travel aboard at the age of 22 and start a new life in the UK. I don’t think he would have thought that ...
Cranfield to JLR: mastering mechatronics for a dream career
My name is Jerin Tom, and in 2023 I graduated from Cranfield with an MSc in Automotive Mechatronics. Originally from India, I've always been fascinated by the world of automobiles. Why Cranfield and the ...
Bringing the vision of advanced air mobility closer to reality
Experts at Cranfield University led by Professor Antonios Tsourdos, Head of the Autonomous and Cyber-Physical Systems Centre, are part of the Air Mobility Ecosystem Consortium (AMEC), which aims to demonstrate the commercial and operational ...
Using grey literature in your research: A short guide
As you research and write your thesis, you might come across, or be looking for, ‘grey literature’. This is quite simply material that is either unpublished, or published but not in a commercial form. Types ...